Purpose
Notice: On December 14, 2021 the Apache Software Foundation notified the community that their initial guidance for CVE-2021-44228 workarounds was not sufficient. We believe the instructions in this article to be an effective mitigation for CVE-2021-44228, but in the best interest of our customers we must assume this workaround may not adequately address all attack vectors.
We expect to fully address both CVE-2021-44228 and CVE-2021-45046 by updating log4j to version 2.16 in forthcoming releases of NSX Intelligence, as outlined by our software support policies. This Knowledge Base article and VMSA-2021-0028 will be updated when these releases are available. Please subscribe to this article to be informed when updates are published.
CVE-2021-44228 and CVE-2021-45046 has been determined to potentially impact VMWare NSX Intelligence Appliance via the Apache Log4js open-source component it ships. This vulnerability and its impact on VMware products are documented in the following VMware Security Advisory (VMSA), please review this document before continuing:
- CVE-2021-44228 & CVE-2021-45046 – VMSA-2021-0028
Impact / Risks
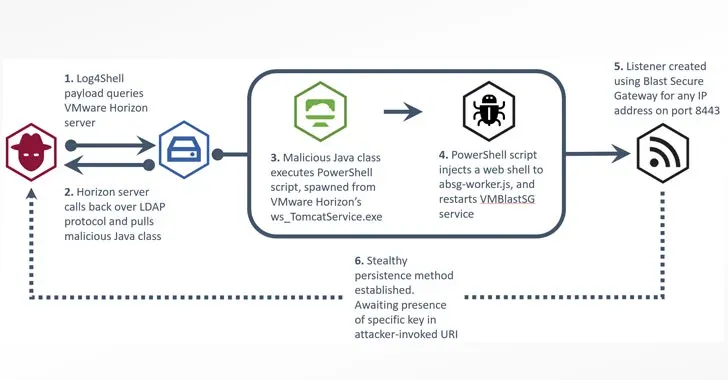
A malicious actor with network access to an impacted VMware product may exploit this issue to invoke remote code execution. There are multiple layers of protection in NSX Intelligence that will make exploiting CVE-2021-44228 & CVE-2021-45046 difficult. Internal NSX Intelligence processes/JVM’s are prevented from making external connections via the iptables configuration in the NSX Intelligence Appliance. However attacker can bypass the protection mechanisms to exploit the vulnerabilities presented by CVE-2021-44228 & CVE-2021-45046.
- Released versions of NSX Intelligence 1.1.x and 1.2.x are exposed to the risk mentioned in CVE-2021-44228 & CVE-2021-45046.
Further exploit of the log message lookup feature may be possible.
Note: If the below workaround is applied to an NSX Intelligence Appliance, and that NSX Intelligence Appliance is subsequently upgraded to a newer vulnerable version of NSX Intelligence, the workaround must be re-applied post upgrade.
Note: This workaround will have to be re-applied on the post-restore NSX Intelligence Appliance if an environment is restored from backup.
Resolution
Upgrades documented in the aforementioned advisory should be applied to remediate CVE-2021-44228 & CVE-2021-45046 when available. Supported versions of NSX Intelligence Appliance will be updated in the near future.
Workaround
To apply the workaround for CVE-2021-44228 & CVE-2021-45046, connect to the VMWare NSX Intelligence Appliance and perform the following steps:
2. Download from ‘zip_3.0-12_amd64.deb’ from the following link http://http.us.debian.org/debian/pool/main/z/zip/zip_3.0-12_amd64.deb
3. Login to the NSX Intelligence Appliance via SSH and using the admin account.
4. Switch to root user:
Enter the root password when prompted.
5. Copy both Debian packages from Step 1 and Step 2 to the NSX Intelligence Appliance. The use of WinSCP, Linux based SCP, or any like method is recommended.
6. Install the Debian package with the following command, run in the directory in which you’ve copied the Debian package to on the NSX Intelligence Appliance. Note: you must install the zip package first.
dkpg -i zip_3.0-12_amd64.deb
dpkg -i nsx-intelligence-log4j2-patch_1.2.1.0.0.19082901_all.deb
7. Reboot the system:
To revert the workaround for CVE-2021-44228 & CVE-2021-45046 to VMware NSX Intelligence Appliance, perform the following steps on the appliance node:
dpkg -r nsx-intelligence-log4j2-patch
Related Information
Change Log:
- December 15th 2021 – 11:30 PST: Added notice acknowledging CVE-2021-45046 and an impending release containing log4j version 2.16.
- December 17th 2021 – 16:30 PST: Added additional zip Debian package to workaround steps.