As of today; 8/6/2021 VMware has released security updates for multiple products to address a critical vulnerability that could be exploited to gain access to confidential information.
Tracked as CVE-2021-22002 (CVSS score: 8.6) and CVE-2021-22003 (CVSS score: 3.7), the flaws affect VMware Workspace One Access (Access), VMware Identity Manager (vIDM), VMware vRealize Automation (vRA), VMware Cloud Foundation, and vRealize Suite Lifecycle Manager.
CVE-2021-22002 concerns an issue with how VMware Workspace One Access and Identity Manager allow the “/cfg” web app and diagnostic endpoints to be accessed via port 443 by tampering with a host header, resulting in a server-side request.
“A malicious actor with network access to port 443 could tamper with host headers to facilitate access to the /cfg web app, in addition a malicious actor could access /cfg diagnostic endpoints without authentication,” the company said in its advisory. Suleyman Bayir of Trendyol has been credited with reporting the flaw.
Response Matrix: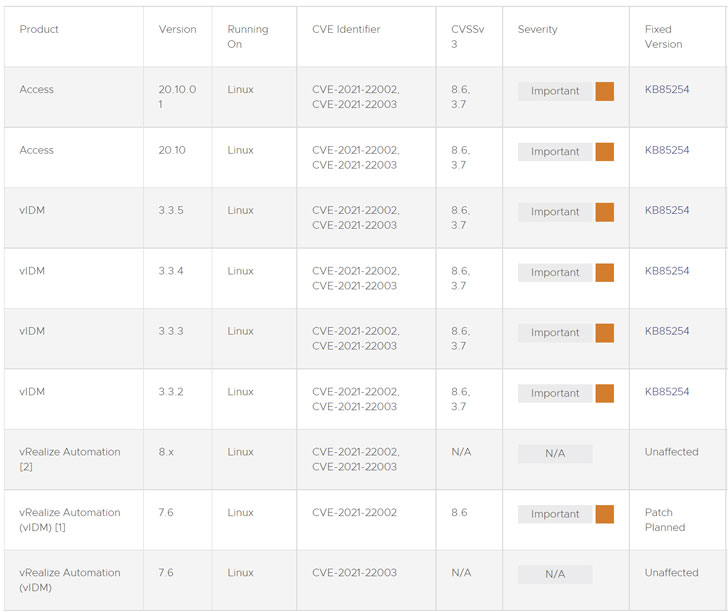
Impacted Product Suites and Components:

Also addressed by VMware is an information disclosure vulnerability impacting VMware Workspace One Access and Identity Manager through an inadvertently exposed login interface on port 7443. An attacker with network access to port 7443 could potentially stage a brute-force attack, which the firm noted: “may or may not be practical based on lockout policy configuration and password complexity for the target account.”
For customers who cannot upgrade to the latest version, VMware is offering a workaround script for CVE-2021-22002 that can be deployed independently without taking the vRA appliances offline. “The workaround disables the ability to resolve the configuration page of vIDM. This endpoint is not used in vRA 7.6 environments and will not cause any impact to functionality,” the company said.
VMware (VMSA-2021-0016) Additional Details:
https://www.vmware.com/security/advisories/VMSA-2021-0016.html
CVE-2021-22002 (CVSS score: 8.6) and CVE-2021-22003 (CVSS score: 3.7)
1. Impacted Products
- VMware Workspace ONE Access (Access)
- VMware Identity Manager (vIDM)
- VMware vRealize Automation (vRA)
- VMware Cloud Foundation
- vRealize Suite Lifecycle Manager
2. Introduction
Multiple vulnerabilities were privately reported to VMware. Patches and workarounds are available to address these vulnerabilities in affected VMware products.
3a. Host header tampering leading to server side request on internal restricted service (CVE-2021-22002)
Description
Known Attack Vectors
A malicious actor with network access to port 443 could tamper with host headers to facilitate access to the /cfg web app, in addition a malicious actor could access /cfg diagnostic endpoints without authentication.
Resolution
Fixes for CVE-2021-22002 are documented in the ‘Fixed Version’ column of the ‘Response Matrix’ below.
Workarounds
Workarounds for CVE-2021-22002 are documented in the ‘Workarounds’ column of the ‘Response Matrix’ below.
Additional Documentation
None.
Notes
[1] vRealize Automation 7.6 is affected since it uses embedded vIDM.
[2] vRealize Automation 8.x is unaffected since it does not use embedded vIDM. If vIDM has been deployed with vRA 8.x, fixes should be applied directly to vIDM.
Acknowledgements
VMware would like to thank Suleyman Bayir of Trendyol for reporting this issue to us.
3b. Information Disclosure Vulnerability (CVE-2021-22003)
Description
Known Attack Vectors
A malicious actor with network access to port 7443 may attempt user enumeration or brute force the login endpoint, which may or may not be practical based on lockout policy configuration and password complexity for the target account.
Resolution
Fixes for CVE-2021-22003 are documented in the ‘Fixed Version’ column of the ‘Response Matrix’ below.
Workarounds
None.
Additional Documentation
None.
Notes
[2] vRealize Automation 8.x is unaffected since it does not use embedded vIDM. If vIDM has been deployed with vRA 8.x, fixes should be applied directly to vIDM.
Acknowledgements
None.
Response Matrix:
| Product | Version | Running On | CVE Identifier | CVSSv3 | Severity | Fixed Version | Workarounds | Additional Documentation |
|
Access
|
20.10.01
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
Access
|
20.10
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vIDM
|
3.3.5
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vIDM
|
3.3.4
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vIDM
|
3.3.3
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vIDM
|
3.3.2
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vRealize Automation [2]
|
8.x
|
Linux
|
CVE-2021-22002, CVE-2021-22003
|
N/A
|
N/A
|
Unaffected
|
N/A
|
N/A
|
|
vRealize Automation (vIDM) [1]
|
7.6
|
Linux
|
CVE-2021-22002
|
8.6
|
Important
|
Patch Planned
|
None
|
|
|
vRealize Automation (vIDM)
|
7.6
|
Linux
|
CVE-2021-22003
|
N/A
|
N/A
|
Unaffected
|
N/A
|
N/A
|
Impacted Product Suites that Deploy Response Matrix Components:
| Product | Version | Running On | CVE Identifier | CVSSv3 | Severity | Fixed Version | Workarounds | Additional Documentation |
|
VMware Cloud Foundation (vIDM)
|
4.x
|
Any
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
|
|
vRealize Suite Lifecycle Manager (vIDM)
|
8.x
|
Any
|
CVE-2021-22002, CVE-2021-22003
|
8.6, 3.7
|
Important
|
None
|
None
|
4. References
Fixed Version:
https://kb.vmware.com/s/article/85254
Workarounds:
https://kb.vmware.com/s/article/85255
Mitre CVE Dictionary Links:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22002
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22003
FIRST CVSSv3 Calculator:
CVE-2021-22002 – https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:L/A:L
CVE-2021-22003 – https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:N/A:N
5. Change Log
2021-08-05 VMSA-2021-0016
Initial Security Advisory
6. Contact
E-mail list for product security notifications and announcements:
https://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce@lists.vmware.com
E-mail: security@vmware.com
PGP key at:
VMware Security Advisories
https://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
VMware Security & Compliance Blog
https://blogs.vmware.com/security
Copyright 2021 VMware Inc. All rights reserved.